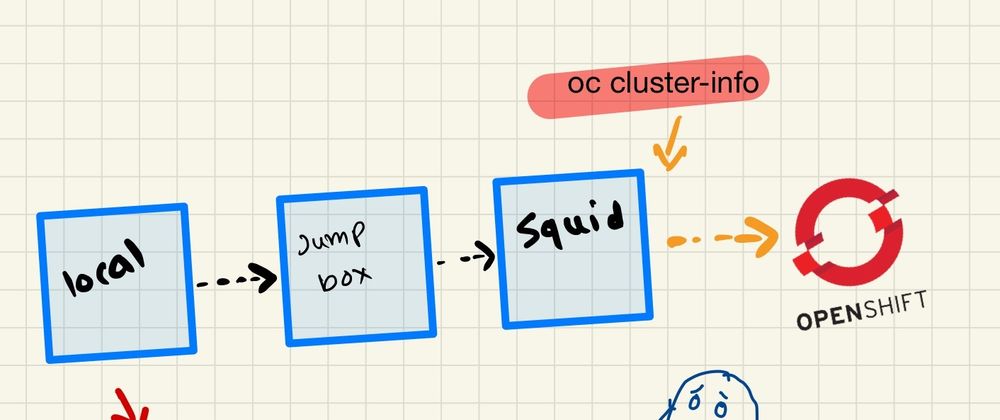
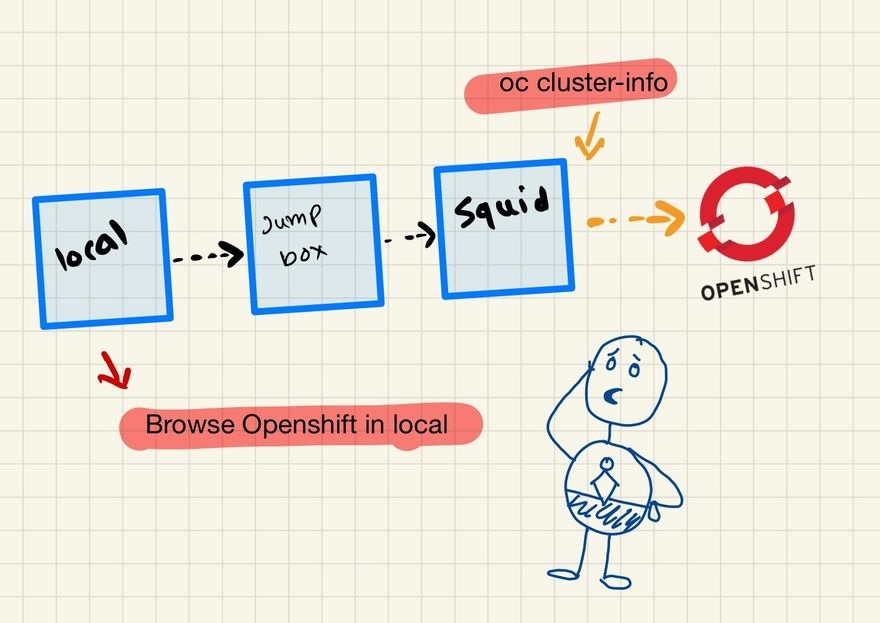
Squid is a widely used open-source proxy server that provides caching and forwarding of HTTP, HTTPS, and FTP web requests between clients and servers. In today's digital world, where data privacy and security are paramount, a Squid proxy can be an essential tool in ensuring the safety of your network. In this article, we will discuss how to install and configure Squid proxy on RHEL 8, set up an SSH tunnel to connect to the proxy server, and configure the browser settings to access the OpenShift web console using Squid.
Section 1: Install and Configure Squid Proxy
The first step is to install Squid on your RHEL 8 server. To install Squid, run the following command in your terminal:
sudo dnf install squid
Once the installation is complete, we need to configure Squid. The configuration file for Squid is located in /etc/squid/squid.conf. Open the configuration file using your preferred text editor.
To change the port on which Squid listens for incoming requests, modify the http_port directive. By default, Squid listens on port 3128. Change the port to 2138 by replacing the existing line with the following:
http_port 2138
Save the file and exit the editor.
Next, we can start, stop, or restart Squid using the following commands:
sudo systemctl start squid
sudo systemctl stop squid
sudo systemctl restart squid
We can use the acl and http_access directives to block access to a specific website. For example, to block access to example.com, add the following lines to the configuration file:
acl blocked_sites dstdomain .example.com
http_access deny blocked_sites
Save the file and restart Squid to apply the changes.
Section 2: Set up an SSH Tunnel to Connect to the Proxy Server
We can set up an SSH tunnel to securely connect to the Squid proxy server. An SSH tunnel is a secure encrypted connection between a local machine and a remote server.
We need to create an SSH configuration file on our local machine. The SSH configuration file is located in ~/.ssh/config. Open the file using your preferred text editor.
Add the following lines to the configuration file:
Host jumphost
Hostname jumphost.example.com
User username
IdentityFile ~/.ssh/id_rsa
ForwardAgent yes
Host squidproxy
Hostname squidproxy.example.com
User username
IdentityFile ~/.ssh/id_rsa
ProxyCommand ssh -W %h:%p jumphost
LocalForward 2138 localhost:2138
Replace jumphost.example.com with the hostname or IP address of your jumphost and username with your username.
Save the file and exit the editor.
To connect to the Squid proxy server, run the following command in your terminal:
ssh squidproxy
This will create an SSH tunnel between your local machine and the Squid proxy server.
Section 3: Configure Browser Settings to Access OpenShift Web Console
To access the OpenShift web console using Squid, we need to configure the browser settings to use the Squid proxy server.
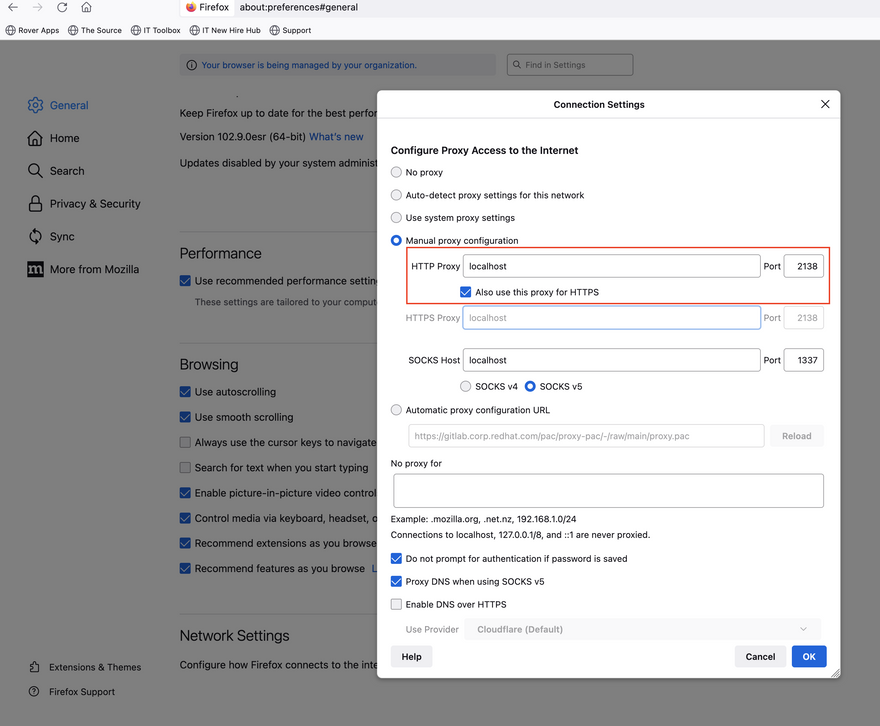
Open your browser and go to the settings. Under the network settings, find the proxy settings, and select "Manual Proxy Configuration." Enter localhost and 2138 as the proxy server and port, respectively.
Additionally, we need to add entries in the /etc/hosts file to map the hostname of the OpenShift web console to the IP address of the keepalived as follows,
192.168.7.144 api.hubztp.telco.ocp.run
192.168.7.145 oauth-openshift.apps.hubztp.telco.ocp.run
192.168.7.145 console-openshift-console.apps.hubztp.telco.ocp.run
192.168.7.145 downloads-openshift-console.apps.hubztp.telco.ocp.run
192.168.7.145 canary-openshift-ingress-canary.apps.hubztp.telco.ocp.run
192.168.7.145 alertmanager-main-openshift-monitoring.apps.hubztp.telco.ocp.run
192.168.7.145 prometheus-k8s-openshift-monitoring.apps.hubztp.telco.ocp.run
192.168.7.145 prometheus-k8s-federate-openshift-monitoring.apps.hubztp.telco.ocp.run
192.168.7.145 thanos-querier-openshift-monitoring.apps.hubztp.telco.ocp.run





Top comments (0)